
From New Dawn 177 (Nov-Dec 2019)
Power is a peculiar thing. In different ways, we’ve become accustomed to co-existing with it and will even forgo some liberties as part of a Faustian trade-off for various modern conveniences. When that power is virtually invisible, it is beyond scrutiny; and when it’s transnational, it takes on a whole new dimension. We are now fast approaching a point in history where opaque structures of power pose a direct threat to our hard-fought-for constitutional and democratic institutions.
Former US National Security Agency (NSA) and Central Intelligence Agency (CIA) analyst turned whistleblower Edward Snowden offered the general public their first real glimpse of this new reality, back in 2013, when he leaked the largest single classified document dump in history. He revealed what could only be described as a vast international conspiracy, in which multiple Western intelligence agencies work hand-in-hand collecting and analysing the personal data of their citizens, completely side-skirting any domestic laws guarding our right to privacy and due process. This ‘conspiracy’ plays a pivotal role in backing-up various allied deep states around the world.
The operational core of this digital syndicate is known as the Five Eyes alliance. Code named FVEY, it represents an international signals intelligence (SIGINT) and communications intelligence (COMINT) gathering agreement between the United States, United Kingdom (UK), Canada, Australia and New Zealand. The Five Eyes alliance agencies include, but are not limited to, the US’s NSA and CIA, the UK’s Government Communications Headquarters (GCHQ), Canada’s Communications Security Establishment Canada (CSEC), the Australian Signals Directorate (ASD), and New Zealand’s Government Communications Security Bureau (GCSB).
This cooperative intelligence-sharing arrangement traces its historical roots to the UKUSA Agreement of 1946, as generally agreed in the 1941 Atlantic Treaty signed between the Allied powers during World War Two.
After its official status was announced in 1955, the Five Eyes was expanded to the Nine Eyes, which includes the original five members along with four additional partnering governments who are granted “third party status.” These include spying agencies from Denmark, France, the Netherlands, and Norway.
The Nine Eyes would later expand to a Fourteen Eyes agreement which includes the Nine Eyes plus Germany, Belgium, Italy, Spain, and Sweden. Not surprisingly, the Fourteen Eyes more or less corresponds with the core European members in the NATO military alliance. The Fourteen Eyes may also be extended up to 17 Eyes when considering other regular third party contributors like Japan, Singapore, and Israel.

In the late 1960s, the Five Eyes launched the ECHELON program, powered by a global array of US-run satellites and SIGINT bases located in North America, Europe, Asia, and Australia. Initially, the Five Eyes arrangement was ideally suited for the Cold War where the primary task was gathering intelligence from the former Soviet bloc countries and their allies. Later, as the internet expanded, the sheer volume of digital content and communications meant that the Five Eyes had to readjust its core competency – from an organisation mainly preoccupied with spying on governments, institutions, and persons of interest, to an organisation whose primary task was to spy on absolutely everyone. With this new raison d’être in mind, the Five Eyes cooperative framework became ideal for allowing spy agencies to bypass domestic laws that might prohibit them from conducting surveillance or hacking their country’s own citizens. Overcoming legal or technical barriers became fairly straightforward, especially in the wake of the attacks of 9/11. The USA Patriot Act meant that intelligence and law enforcement agencies could invoke national security and require telecoms companies and internet service providers (ISPs) to allow fibre optic splitters to be installed at key nodes in the telecommunications infrastructure, allowing spooks to divert massive data flows to be captured and run through the various Five Eyes data analysis centres.

alliance.
The digital revolution gave the Five Eyes syndicate the ability to amalgamate and combine what was previously separate disciplines of intelligence – like SIGINT, COMINT, geospatial and human intelligence – now all rolled into one comprehensive data collection system. Once they reached this stage, getting it to perform was simply a case of tweaking the software. When Snowden’s story broke in 2013, one of the key components of the NSA’s mass surveillance operation was a software interface called XKEYSCORE. The Intercept describes the tool as follows:
The sheer quantity of communications that XKEYSCORE processes, filters and queries is stunning. Around the world, when a person gets online to do anything – write an email, post to a social network, browse the web or play a video game – there’s a decent chance that the internet traffic her device sends and receives is getting collected and processed by one of XKEYSCORE’s hundreds of servers scattered across the globe.
Whereas previous iterations of the NSA’s global information dragnet hauled in large quantities of data and required a combination of computer and human intelligence to sift through it all, XKEYSCORE “extracts and tags metadata and content from the raw data so that analysts can easily search it,” allowing for a much more refined and efficient data capture operation. In essence, what used to be done by the entire ECHELON system and scores of human analysts could now be achieved with a few strokes of the keyboard.

Spectre is Real
Michael McKinley of the Australian National University, in an article describing the full scope of the NSA’s digital arsenal, mentions “[t]he known codewords for them over recent times: Blarney, Echelon, Dancingoasis, PRISM, Tempora, XKEYSCORE [sic], Muscular, Pinwale, EgotisticalGiraffe, Stormbrew, Fairview, Oakstar, Mainway, Rampart-T, and Nucleon. Between them, they aim to attack computers using certain types of legal privacy software, and overall to harvest, store, and analyse whatever internet traffic can be hoovered up.”
Imagine if the NSA connected all of these data trawling nodes with an artificial intelligence backbone that analysed and parsed out teraflops of information in real-time. It would make the agency omnipotent. This very same dystopian scene was brought to life on the big screen in the 2015 James Bond film Spectre starring Daniel Craig. In the film, a latter-day Blofeld, played by actor Christoph Waltz, devised a new unofficial international ruling committee, S.P.E.C.T.R.E. (Special Executive for Counter-intelligence, Terrorism, Revenge and Extortion), comprised of the world’s top organised crime figures. Through his network’s infiltration of the very top levels of Western intelligence, Blofeld receives unrestricted, real-time access to all surveillance data collected by the “Nine Eyes” countries. This backdoor key gives Blofeld the power to steer global political events, move markets, and when necessary, blackmail any individual or institution into compliance.
Aside from its striking parallel to the West’s current global surveillance dragnet, Spectre raises important questions obscured by the film’s ostentatious plot. Even without Blofeld, the current Nine Eyes intergovernmental network retains all of the capabilities that any nefarious villain would ever want, to wield power or ward off any potential challengers. If operations are conducted outside public view, then the potential for abuse is virtually boundless.
Five Eyes: A Fraternal Order
The fraternal nature of SPECTRE was alluded to by the antagonist’s cinematic forefather, Ernst Stavro Blofeld, depicted in the 1963 Bond film Thunderball. “SPECTRE is a dedicated fraternity whose strength lies in the absolute integrity of its members,” said Bond’s nemesis.
Blofeld wasn’t wrong. In essence, the Five Eyes intelligence network is precisely that – a type of Anglo-fraternal organisation that wields a noticeable advantage over its rivals. Such unfettered cooperation between advanced nations like the US, UK, Canada, Australia and New Zealand, means that the technical continuity of this geopolitical alliance remains more or less unmatched. Leveraging the resources of five countries spread around the globe affords the coalition a substantive advantage over just about any other global competitor. No other bloc can match its scope and scale, geographically and technologically.
It is also fundamentally neo-colonial in nature. The fact that this network comprises current and former British colonial possessions speaks to the Anglo-centric or Atlanticist worldview on which its mission is based. That Atlanticist agenda is best described as something akin to a Bilderberg Committee agenda – a set of political and industrial objectives and goals informally agreed upon by some of Western society’s most powerful luminaries and technocrats who meet at the beginning of summer at the annual Bilderberg Meeting.
Interestingly, this fraternal brotherhood only seems to extend to certain allies. While German spy agencies like the Bundesnachrichtendienst (BND) cooperate with their US counterparts as a “third party” government through the Fourteen Eyes agreement, Washington spooks still feel the need to constantly spy on Berlin. The 2013 Snowden leaks revealed that Germany is a major target of US espionage run out of the NSA’s own European Cryptologic Center (ECC), known affectionately as the “Dagger Complex,” located in Griesheim, in the German state of Hesse.
According to “secret” NSA documents viewed by the German publication DER SPIEGEL, the American bunker accounts for the agency’s “largest analysis and productivity in Europe.” The documents also note that the NSA uses its infamous XKEYSCORE software to trawl up its main areas of interest from inside the German government, namely foreign policy, economic stability, new technologies, advanced weaponry, arms exports, and international trade.
To add insult to injury, WikiLeaks revealed in 2015 that the phone of German Chancellor Angela Merkel had been wiretapped for years by US spies.
When interviewed on the matter, former NSA and CIA head Michael Hayden was quite flippant, openly admitting, “We steal secrets. We’re number one in it…. But, he adds, this is not malicious or industrial espionage…. We steal stuff to make you safe, not to make you rich.”
Hayden lamented the German disclosure but admitted the US government had grossly underestimated German values on issues pertaining to privacy, stating:
Perhaps we underestimated the depth of feelings that the German people – and again, not just the chancellor, but the German people, felt about this question of privacy, given their historical circumstances compared to our historical circumstances. At the Munich Security Conference it was clear to me that Germans regard privacy the way we Americans might regard freedom of speech or religion.
In similar fashion, both the European Union and the United Nations are also said to be under US surveillance. Like with Germany, NSA espionage objectives on the EU include foreign policy goals, the economy, international trade, and “energy security.” The targeting of the UN adds a whole other international dimension to these operations. A 2013 report filed by The Guardian newspaper paints a rather disturbing picture: “[L]ong before [former United Nations Secretary-General] Ban’s limousine had even passed through the White House gates for the meeting, the US government knew what the secretary general was going to talk about, courtesy of the world’s biggest eavesdropping organisation, the National Security Agency.”
Australia: Casualty in a Cold War
On the surface, having the NSA conduct surveillance operations on key allies like Germany may not make much sense. Why would America risk compromising an important relationship with a pivotal partner and fellow NATO member? To help answer that question, we need to go back 50 years and look at what happened in Australia circa 1970.
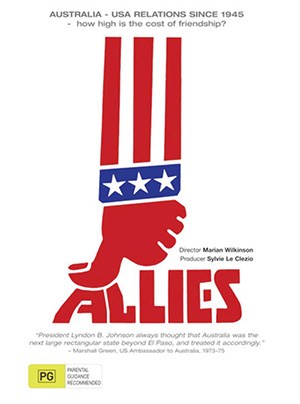
www.roninfilms.com.au/feature/9916/allies.html).
In the groundbreaking documentary film Allies (1983), a number of top former US and Australian politicians and intelligence officials went on camera to recount one of the most tumultuous periods in the country’s history during the Cold War, marked by the establishment of the Australian Security Intelligence Organisation (ASIO).
The film disclosed a series of shocking admissions rarely heard before in public, but which lifted the veil on the hidden hierarchy latent within the Five Eyes order. Revelations included an admission by Victor Marchetti, former executive assistant to the deputy director of the CIA (1955-1969), who stated: “Intelligence organisations in many countries have a loyalty that is not necessarily to the duly constituted government, they have a loyalty to what they consider the establishment.” Some officials testified that their loyalty was not to their elected leaders but the CIA.
Such testimony provides some of the most unequivocal evidence to date about the existence of an unelected shadow government or Deep State, directed by America’s Central Intelligence Agency. For the Americans, managing this autonomous power structure first meant securing its geostrategic interests in host countries as well as its strategic facilities like the NSA’s Pine Gap listening base located in central Australia. Securing these assets became a national security issue – Washington could not risk any newly elected government interfering with US intelligence operations.
In the film, Dr John Burton, Secretary of the Australian government Department of External Affairs (1947-1950), described the Five Eyes thinking as follows:
…the need for an intelligence organisation was to ensure that governments elected (for example) on a social welfare platform would not argue that they had a mandate to recognise China, to change the agreement with the United States, or other things which the Labor Party had intended before the Petrov Commission. They’ve always argued that the intelligence operation, or the intelligence services, operating as an informal group – are the protection of democracy against itself.
While the notorious Petrov Affair (1954) helped sideline Australia’s Labor party for many years afterwards, the real trigger for a US-backed coup came in 1972 when Gough Whitlam led Labor to victory for the first time in 23 years. The Whitlam government called into question Australia’s supporting roles in various military conflicts taking place in Southeast Asia, including Vietnam and Indonesia, and challenged the top-secret nature of US bases operating in Australia. Details of a CIA plot to depose Whitlam were revealed by NSA contractor Christopher Boyce, who was convicted of espionage and sentenced to federal prison in the US. Boyce’s story was later made into a cinematic classic, The Falcon and the Snowman.
Whitlam would soon be removed from office in 1975 after being “dismissed” by the country’s Governor-General, with much of the evidence pointing to a US/British regime-change operation. This marked a noticeable shift to the right in Australian politics and an unflinching “special relationship” with subsequent US Administrations.
This story demonstrates the lengths that the US-led Five Eyes syndicate is willing to go to secure its assets in foreign countries. In the case of Australia, this meant US intervention to derail any government that might threaten US foreign policy and its global intelligence operations. From this vignette, one could draw a parallel to Washington’s ill-treatment of Germany – another ally that also hosts numerous US military bases and intelligence-gathering facilities, and which functions as an anchor for US operations in Europe in much the same way Australia does for the Asia-Pacific region.
The China Syndrome
In the 21st century, mere national monopolies are no longer sufficient for Silicon Valley moguls and their shepherds in the intelligence community. Firms like Google, Apple, Facebook and Twitter command near-global monopolies in their respective markets. This means that as long as those Western firms permeate and dominate the planetary information space, Five Eyes operatives only require a backdoor into a handful of these firms to surveil and control almost every aspect of public (and even private) life.
Controlling technology markets has become a matter of paramount concern for the Five Eyes. That includes keeping out any foreign product which could cause a wrinkle in their control matrix. As expected, this situation feeds neatly into a ready-made geopolitical drama, especially if the Trojan Horse in question arrives in the form of a Chinese firm.
As Britain expedites the roll-out of its controversial high-frequency 5G network, new security concerns have surfaced at the heart of the Five Eyes as politicians and spooks debate the possibility a foreign actor could compromise the alliance from within.
Western technocrats have rushed to finalise preparations to create a grid of “smart cities” and smart infrastructure including fleets of self-driving cars on “smart highways,” as well as a host of public services – all linked as part of the “internet of things.” To make this project work, the UK has to partner with the only company who can deliver enough advanced equipment on time and on budget – Chinese telecommunications giant Huawei.
In theory, Five Eyes fears may be warranted. With 5G set to provide the new framework for real-time spying and data monitoring, Western spy chiefs and politicians are afraid of becoming too reliant on potential geopolitical and commercial rival China. Practically speaking, Huawei’s hardware is fairly standardised and compatible with other components used to configure the UK’s new 5G network, and to date, there is no proof of any latent Chinese spyware in any of the components in question. UK spy chiefs are already lining up in defence of the realm, with former MI6 head Richard Dearlove chiming in: “…we must conclude the engagement of Huawei presents a potential security risk to the UK. The key question that follows is can that risk be sufficiently mitigated to render it negligible?”
A number of tertiary arguments against Huawei are being employed by Western officials including charges that China steals Western intellectual property, or that Chinese firms are inherently ‘anti-competitive’ because of state subsidies given to many enterprises. Reading between the lines, more of a worry for the Five Eyes (or a privatised Spectre syndicate) is the fact that a whole range of other Huawei products could employ a different proprietary Chinese encryption protocol that would give not only Chinese officials and intelligence workers a privacy edge, but the public mass-consumer too – keeping the NSA from intercepting a user’s communications, or at least making it much more difficult. Thus, keeping Chinese products out of Western surveillance zones could be a major priority for Five Eyes technocrats.
Earlier this year, US President Donald Trump escalated the technology war with China by signing an executive order that prohibits US companies from installing any “foreign-made” telecoms equipment which the US deems a national security threat, meaning that Huawei requires a special license issued at the discretion of Washington. Huawei Chairman Liang Hua responded at an industry press conference during the China-Germany-USA Media Forum, saying that the US placing Huawei on its entity list has had “no substantial impact” on Huawei’s business and that all of the company’s flagship products are shipping as normal.
In the short-term, the Trump Administration is more likely to deploy economic warfare by drastically increasing tariffs on Chinese products. In this war, the winning edge might be with the state-managed economy where Chinese planners typically plot the course ahead looking at 20 to 30-year windows, as opposed to US firms that prioritise mere quarterly gains and shareholder dividends.
Liang Hua remarked that in only two or three years, Huawei will have developed a complete technological and commercial “ecosystem” for its range of products, making it more difficult for the Five Eyes syndicate to maintain their digital hegemony by trying to shut Huawei out of international markets. Naturally, this poses a direct threat to the West’s global digital media and communications mafia, and its overlapping fraternal network of government agencies, corporations and ‘white-collar’ organised criminal syndicates.
The War on Encryption
Aside from concerns about statecraft, most independent-minded citizens might be alarmed by the unbridled Orwellian power of such a global operation. On this point, there is little advice one can offer other than to stay off social media or go ‘off-grid’ (offline) as much as possible to avoid leaving a detailed digital footprint that can be used to build a profile on you.
For those who depend on the internet for their day-to-day existence, going off-grid is not really a practical option, but there are tools available that can help make surveillance difficult for 5, 9, and 14 Eyes member governments. Besides using a reliable encrypted chat or messaging service, if you are not already using a Virtual Private Network (VPN), then now may be a good time to start. VPN encrypts all of your internet traffic and scrambles your IP address, making it difficult for anyone monitoring you online to pinpoint your identity, device, and physical location. One key requirement is trying to use a service based outside the Fourteen Eyes countries. This means you may not be immediately exposed should your service provider’s host country ask for back door access to your internet records. If you are using a service within the Fourteen, then be sure to choose a company that has a ‘no logs’ policy. In other words, should a US or UK agency like the NSA or GCHQ make a formal request from a service provider to hand over all your internet search data, then there will be nothing they can hand over. Likewise, you can use a number of encrypted instant messaging services like Telegram, or encrypted email services like Proton Mail, and also consider using an internet browser that doesn’t keep data on your surfing like Brave, or a search engine like Duck Duck Go which doesn’t save data on all of your search activity.
Perhaps the biggest obstacle to Five Eyes hegemony are digital services that use end-to-end encryption. This means only the sender and receiver can view the content, concealing communications from the prying eyes of Western spy agencies. Needless to say, insatiable state authoritarians are not happy about this and have laid down a harrowing ultimatum to tech companies, demanding write-in backdoor access protocols supposedly for “law enforcement.” If firms do not comply, government officials threaten they should be ready for brute force intrusions by agents of the state. Knowing they do not have the public on their side, governments have resorted to intimidation and scare tactics in order to swing public opinion in their favour.
While served as Home Secretary in 2015, former UK Prime Minister Theresa May authored a rather opprobrious piece of legislation entitled the Investigatory Powers Act (IPA), which outlines where the British police state is heading in terms of privacy and encryption. The bill requires that any “communications service provider” (ISPs, social media platforms, VOIP, email providers and messaging service) must comply with a secret warrant signed by the Home Secretary which names any persons or organisations the government wishes to spy on.
One watchdog organisation who has followed the IPA is the Electronic Frontier Foundation (EFF). According to researchers, the draconian decree, also known as the ‘Snooper’s Charter’, requires tech companies to insert special malware onto their systems so the spooks can use their platforms to “interfere with any other system.” The secret warrant explicitly allows those companies to violate any other laws in complying with the warrant. Essentially, the warrant enables said tech firms to violate the law in the process of complying with the government’s secret snooper’s warrant. This would also include the Home Secretary ordering firms like Facebook, Samsung or Apple to quietly remove their ‘secure communication’ features from products without notifying the public about it.
In terms of its legality (or lack thereof), the devil is in the absence of detail. Danny O’Brien from EFF noted how the UK government has been very careful not to pin itself down with any specifics, explaining, “Sure enough, the word ‘encryption’ does not appear in the Investigatory Powers Act (IPA). That’s because it is written so broadly it doesn’t need to.”
EFF describes the severity of the IPA in terms of riding roughshod over basic civil rights and protections:
“The Investigatory Powers Bill, one of the first laws to explicitly permit such techniques for law enforcement and intelligence work, contains very little in the way of oversight, and grants the British government an almost blank check for deploying malware against individual users as well as the heart of the internet’s infrastructure. It also demands that private companies and individuals assist in the deployment of this spyware, no matter where they operate in the world, and requires that this assistance be kept permanently secret from customers, partners, and the general public.
IPA provisions might also include the government forcing a chain of coffee shops to use the company’s free WiFi service to deploy British spy agency malware against its customers.
The state’s intrusion goes even further with the IPA laying the parameters for the UK government to demand tech companies supply them with new product designs… in advance of commercial release. This is a shocking act of overreach by the British state – one that exceeds even the most invasive state intervention in a country like China.
One has to ask: given the chance, would the UK government eventually pursue a complete ban on encryption?
While there is considerable push-back from tech companies and public advocacy groups, there’s surprisingly little rebellion from most mainline politicians, partly because they are not being pressured from their constituents on this issue. What anti-privacy initiatives like the IPA clearly demonstrate is that Britain is the one clearly setting the dark tone and aggressive pace for the Five Eyes cohort. The agenda clearly seeks a renewed license to put tech firms in a corner by deploying emotive language and invoking evermore dramatic conspiracy claims. In her article written for the Telegraph, current UK Home Secretary Priti Patel even went so far as to equate Facebook’s noncompliance with aiding and abetting “child abusers, drug traffickers and terrorists plotting attacks.”
Of course, Patel’s comments shouldn’t surprise anyone who has followed the issue of privacy over the years, particularly in the post-9/11 era where politicians and national security state operatives routinely gaslight the public to justify every intrusion or roll-back of privacy rights by citing the most extreme and infrequent instances of ‘terrorism’. For the 21st century technocracy and police state, that’s been the gift that just keeps giving, but by the same token the public have become increasingly wary of such dramatic government claims due to the fact that very rarely, if ever, has government wiretapping or backdoor spying actually thwarted a terrorist attack in what is popularly referred to in national security rhetoric and Hollywood propaganda lore as ‘the ticking bomb’ scenario.
According to a report by security experts Sophos, at a recent Five Eyes security summit officials left no doubt as to their intentions, stating: “Tech companies should include mechanisms in the design of their encrypted products and services whereby governments, acting with appropriate legal authority, can obtain access to data in a readable and usable format.”
Five Eyes member Australia took the matter even further, threatening to “break in” if tech companies do not facilitate the access requirements of the state. This new policy initiative was expressed unabashedly in a memo issued by the Australian Dept of Home Affairs on behalf of the Five Eyes alliance:
The Governments of the Five Eyes encourage information and communications technology service providers to voluntarily establish lawful access solutions to their products and services that they create or operate in our countries…. Should governments continue to encounter impediments to lawful access to information necessary to aid the protection of the citizens of our countries, we may pursue technological, enforcement, legislative or other measures to achieve lawful access solutions.
A closer look at the memo reveals that Australia’s authoritarian designs are not restricted to stopping terrorists and paedophiles but appear to target any entities they feel are “sowing discord” (including any popular dissenting opinion and analysis), that supposedly threatens our vaunted “democratic institutions.” This may also include any foreign media (as depicted in the heavily promoted ‘Russian disinformation’ narrative), independent media, and free-thinking individuals on social media. The language could not be more arbitrary:
We are determined to ensure that the technologies that have been developed to enhance prosperity and freedom are not exploited by those who seek to promote terrorism and violent extremism; prey upon and exploit our children; or spread disinformation and discord to undermine our democratic institutions.
This, alongside Britain’s notorious ‘Snooper’s Charter’, demonstrates how Five Eyes partners are working in concert by gradually laying down an alliance-wide legal framework that will legitimise what would normally be unwarranted activity by state agencies. This is done by suspending any constitutional provisions or rights – all in the name of protecting national security, or even the national interest as the state defines it.
Many leading VPNs and messaging services can protect your data with 256-bit encryption, now used in most modern encryption algorithms and protocols. For the moment, this technology offers fairly robust protection from the prying eyes of the intelligence services, but advances in computing power may eventually put many of these protections at grave risk. New advances in quantum computing threaten to usher in a new event horizon whereby the next generation of computers could conceivably crack today’s industry-standard 256-bit encryption key in a relatively short period of time – in mere minutes, or even seconds. Researchers at the Massachusetts Institute of Technology (MIT) have shown how a quantum processor can crack a seemingly impenetrable 2,048-bit RSA encryption in only eight hours. Exactly how far off we are to this quantum revolution is anyone’s guess but when it arrives it could tip the scales of privacy away from the consumer and in favour of those organisations who control this new technology, namely Silicon Valley monopolists and the intergovernmental Five Eyes complex. On the flip side, advances in quantum decryption may also coincide with new methods of encryption that could slow down quantum crackers enough to make decryption impractical.
It’s incredible to think that these technological battles waged in binary virtual space may end up defining our relationship with the state in the physical world.
Things are moving extremely fast right now. Such a dystopic state of affairs must be resisted on every level. Our future depends on it.
Footnotes
1. UKUSA Agreement Release (1940-1956),www.nsa.gov/news-features/declassified-documents/ukusa/
2. A Look at the Inner Workings of NSA’s XKEYSCORE, www.theintercept.com/2015/07/02/look-under-hood-xkeyscore/
3. The unsettling reality if Five Eyes is the guardian against Huawei (Part 2), www.johnmenadue.com/michael-mckinley-the-unsettling-reality-if-five-eyes-is-the-guardian-against-huawei-part-2-a-survey-audit-concerning-prudence-integrity-law-and-ethics/
4. US Intelligence Watches Germany Closely, www.spiegel.de/
international/world/germany-is-a-both-a-partner-to-and-a-target-of-nsa-
surveillance-a-916029.html
5. NSA tapped German Chancellery for decades, WikiLeaks claims, www.
theguardian.com/us-news/2015/jul/08/nsa-tapped-german-chancellery-
decades-wikileaks-claims-merkel
6. Shame on US, www.spiegel.de/international/world/spiegel-interview-with-former-nsa-director-michael-hayden-a-960389-2.html
7. Portrait of the NSA: no detail too small in quest for total surveillance,
www.theguardian.com/world/2013/nov/02/nsa-portrait-total-surveillance
8. Huwaei, 5G and the Five Eyes, www.henryjacksonsociety.org/shop-hjs/defending-our-data-huawei-5g-and-the-5-eyes/
9. US blacklists Huawei, places it on entity list, www.economictimes.
indiatimes.com/news/international/business/us-blacklists-huawei-places-it-on-entity-list/articleshow/69353632.cms
10. Twitter, twitter.com/HuXijin_GT/status/1176465008974123008
11. Five Eyes Unlimited: What A Global Anti-Encryption Regime Could Look Like, www.eff.org/deeplinks/2017/06/five-eyes-unlimited
12. UK Investigatory Powers Bill, www.eff.org/issues/uk-investigatory-powers-bill
13. Facebook’s encryption could stop our police doing their job properly –
and I won’t allow that to happen, www.telegraph.co.uk/politics/2019/07/30/facebooks-encryption-could-stop-police-job-properly-wont-allow/
14. What’s the Evidence Mass Surveillance Works? Not Much, www.pro
publica.org/article/whats-the-evidence-mass-surveillance-works-not-much
15. Five Eyes nations demand access to encrypted messaging,www.naked
security.sophos.com/2019/08/01/five-eyes-nations-demand-access-to-
encrypted-messaging/
16. Five Country Ministerial 2018, www.homeaffairs.gov.au/about-us/our-port
folios/national-security/security-coordination/five-country-ministerial-2018
17. MIT Technology Review, www.technologyreview.com/s/613596/how-a-quantum-computer-could-break-2048-bit-rsa-encryption-in-8-hours/
18. Why Quantum Computers Might Not Break Cryptography, www.quanta
magazine.org/why-quantum-computers-might-not-break-cryptography-20170515
© New Dawn Magazine and the respective author.
For our reproduction notice, click here.